Endor Labs detects malware in dependencies by scanning the packages used in the project and recognizing known malicious patterns.
Monitoring for Known Malicious Packages: Scan dependencies to identify malware by cross-referencing findings with the Open Source Vulnerability (OSV) database.
Suspicious Code Behavior: Use malware detection rules and Semgrep-based rules to scan open source packages dependencies for suspicious code patterns and behaviors. These rules analyze code structures, detect anomalies, and identify potential threats.
Classification of malware
When Endor Labs detects known malware in your dependencies, it raises a critical priority finding in your namespace for immediate remediation.
If a suspicious code pattern is detected in a dependency, a low priority finding is raised, and a security score is assigned to the package. Our security team evaluates the finding based on multiple factors, such as the nature of the detected pattern and its potential impact. If confirmed as malware, a critical priority finding is raised in your namespace and reported to you. Otherwise, it is dismissed as a false positive.
See Security score for more information.
View malware findings
You can view the malware findings, prioritize them, and take corrective action.
- Sign in to Endor Labs and select Projects from the left sidebar.
- Select the project for which you want to view the malware.
- Select Malware under Code Dependencies to view malware findings.
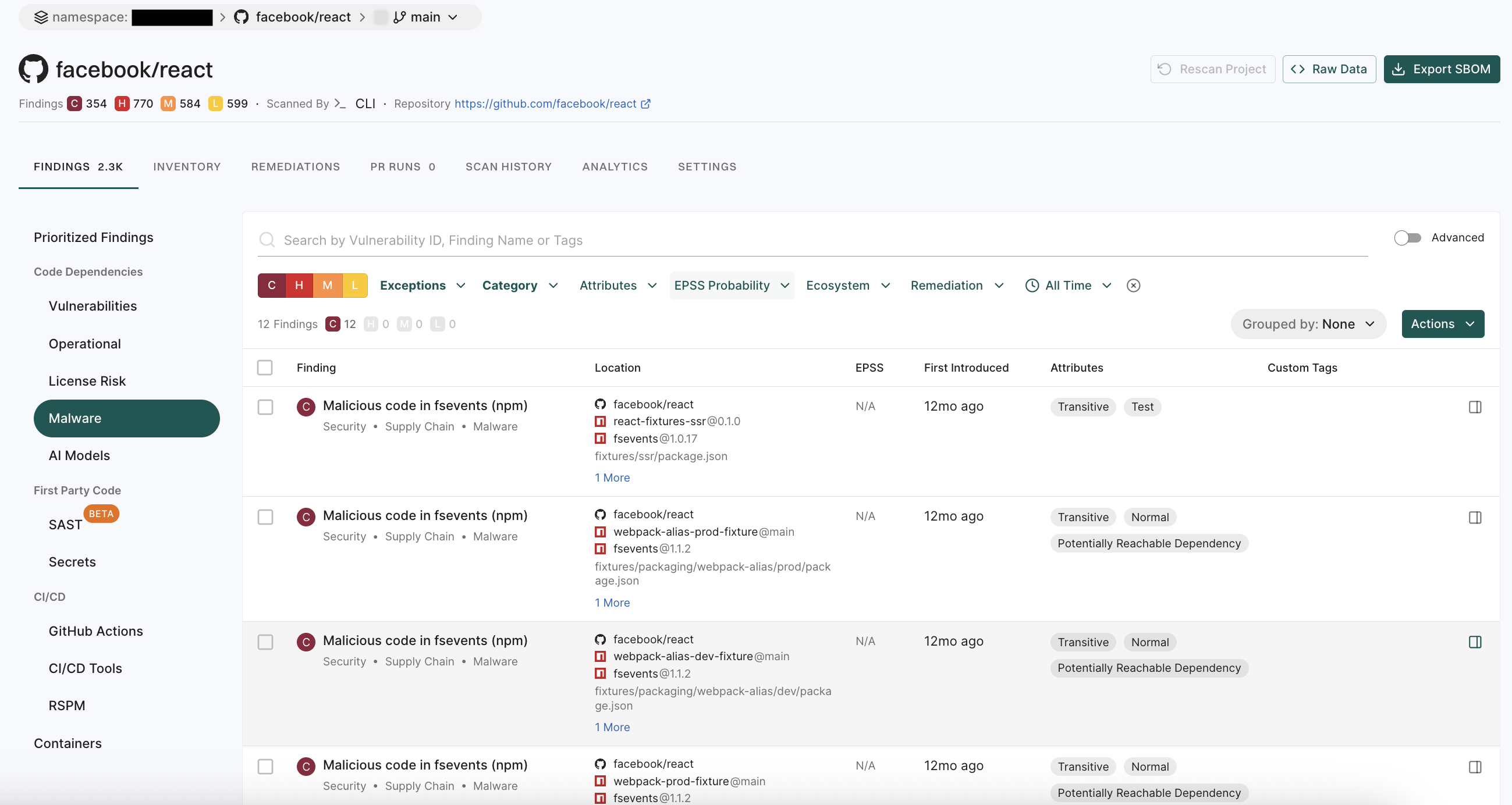
-
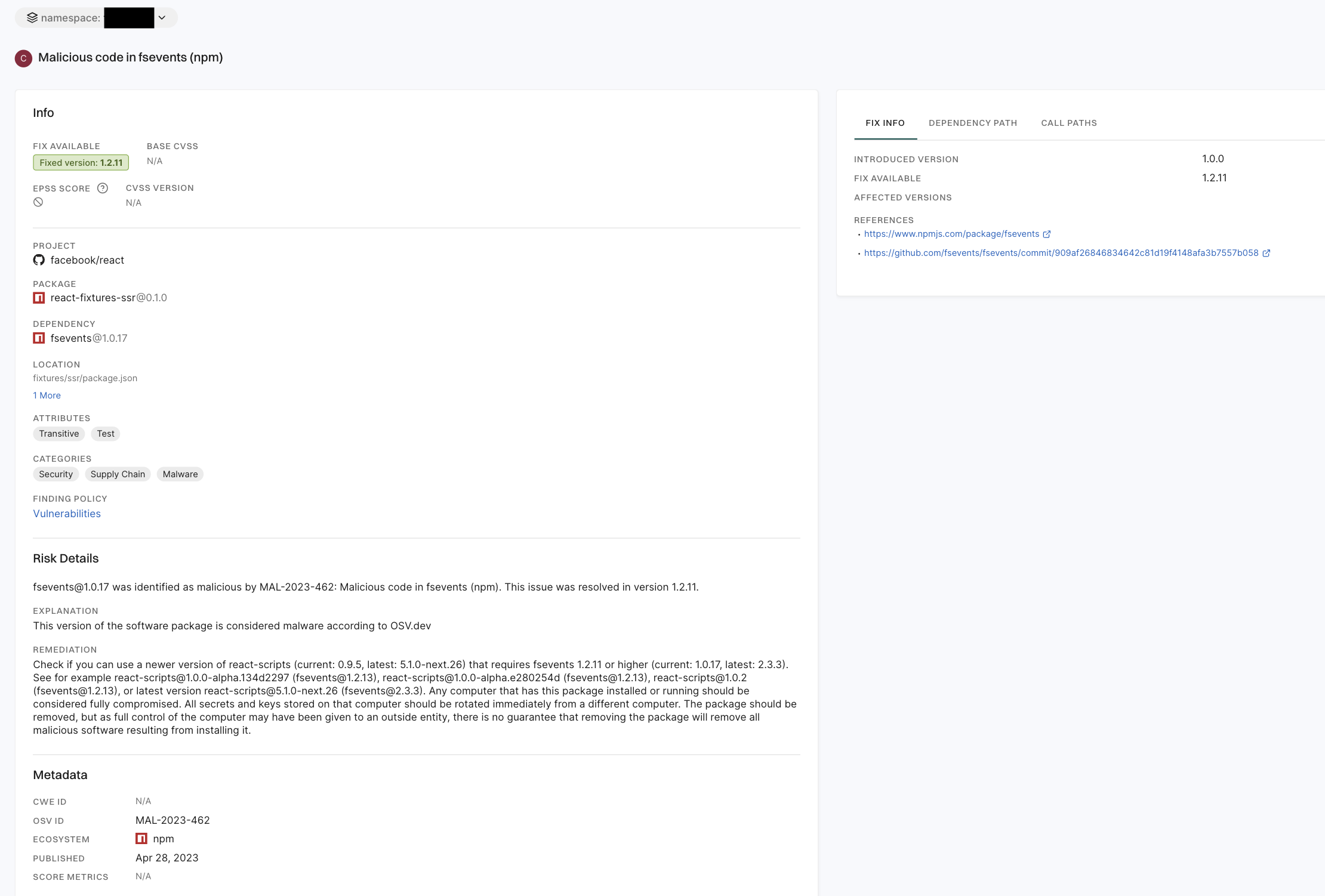
Select a finding to view detailed information of the malware in the right sidebar.
The right sidebar contains the following information:
- Project: The name of the project where the malware is found, finding policy, categories and attributes of the project.
- Risk Details:
- Indicates if the identified secret is valid or invalid.
- Explanation of the finding.
- Recommended remediation.
- Metadata: Contains details such as the vulnerability ID, ecosystem, publication date, and security metrics.
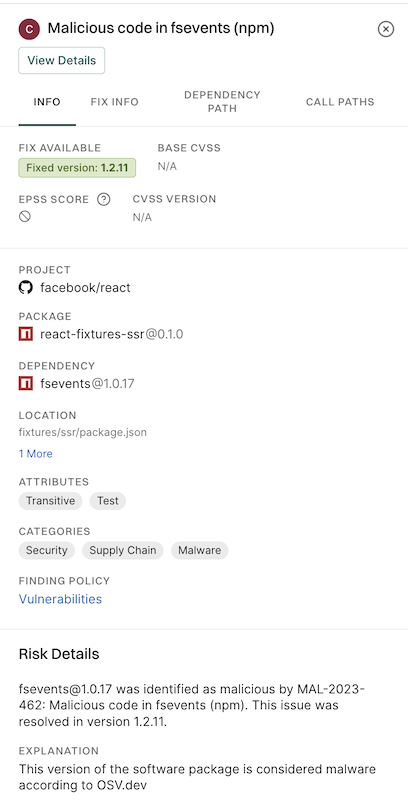
- Click View Details to explore additional information about the malware findings such as FIX INFO, DEPENDENCY PATH, and CALL PATHS.